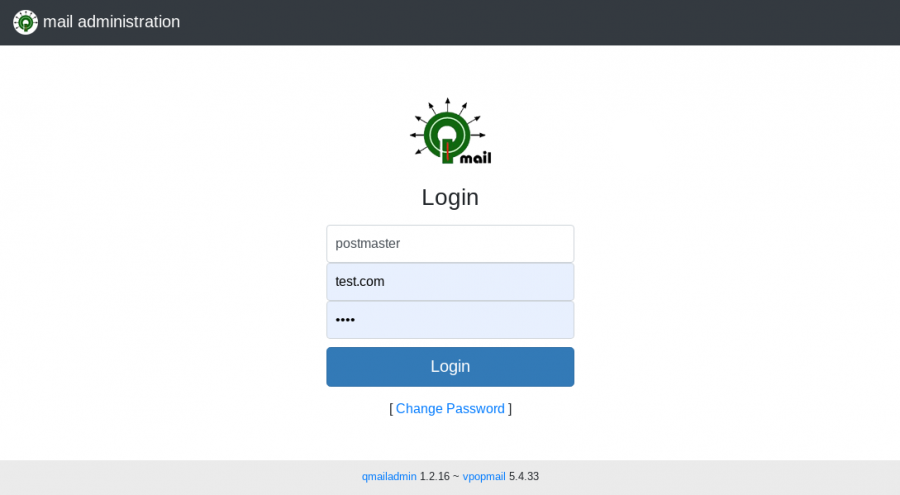
qmailadmin
March 27, 2024 by Roberto Puzzanghera 121 comments
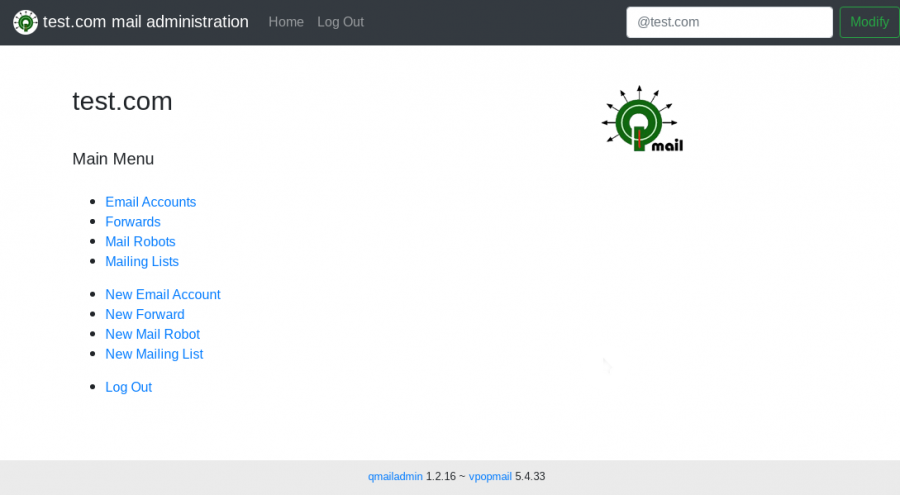
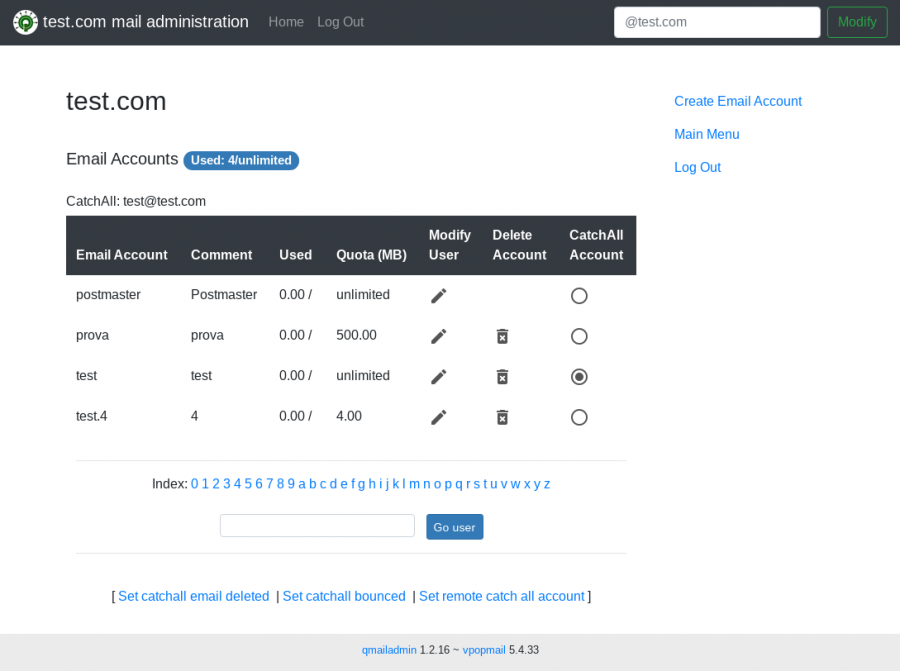
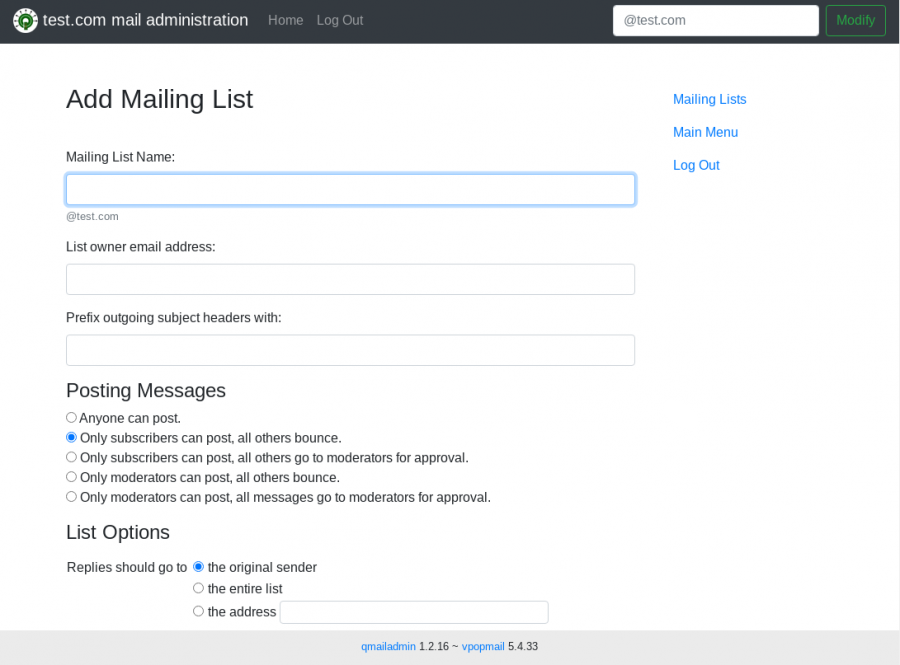
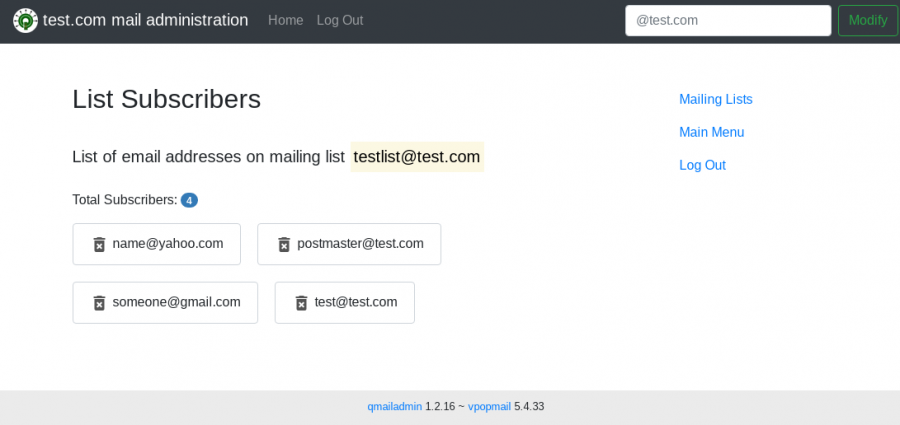
qmailAdmin is a free software package that provides a web interface for managing a qmail system with virtual domains. It provides admin for adding/deleting users, Aliases, Forwards, Mailing lists and Autoresponders.
As you can see, for convenience I moved the qmailadmin sources to my github space. Nonetheless, all information about qmailadmin will continue to be posted here, and this page remains the place to seek support if needed.
This qmailadmin puts togheter the original Inter7's 1.2.16 version with the following patches (updated to 2023.08.27 old patch version):
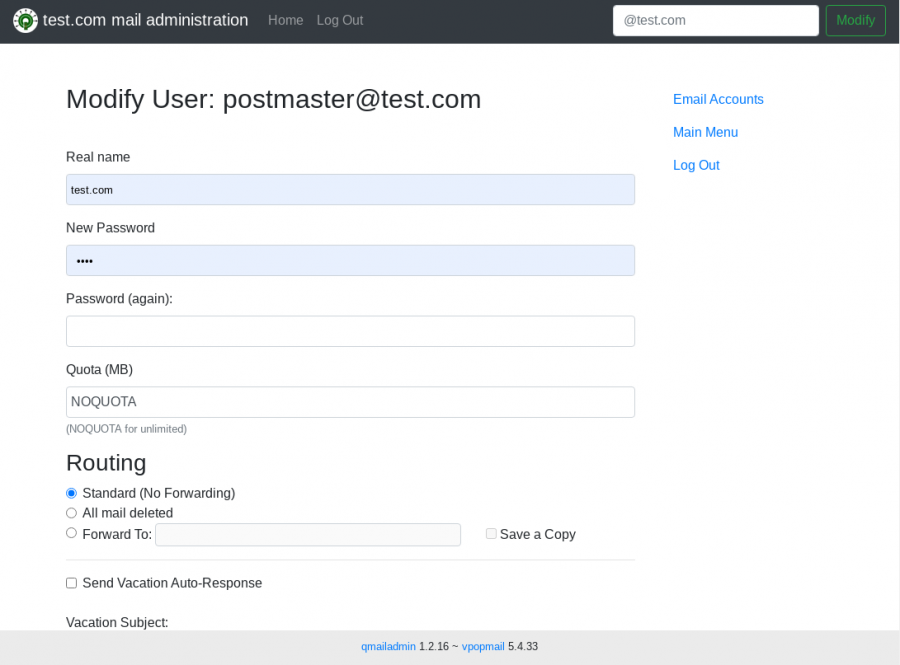
- qmailadmin-skin, a patch that I created during covid-19 spare time, provides a new responsive skin to the control panel. It modifies everything under the html dir and many .c files in order to adjust the
htmlembedded into the source files. Added a style sheet in the "images" folder and a couple of png files for theqmaillogo. It will be much easier to modify theqmailadmin's skin from now on. - A patch to call
cracklibin order to check for the password strenght. This should avoid unsafe accounts created by domain administrators such as "test 123456". - A nice patch (thanks to Tony, original author unknown) which gets
qmailadminto have authentication failures logged. This makes possible to ban malicious IPs viafail2ban. It is required to create the log file /var/log/qma-auth.log initially and assign write priviledges toapache. - ezmlm-idx 7 compatibility patch (author unknown), which restores the compatibility with
ezmlm-idx-7(thanks to J.D. Trolinger for the advice). - a fix to the catchall account (thanks to Luca Franceschini).
- another fix to autorespond.c to correct the way the
.qmailfiles are modified
Roundcube webmail
February 14, 2024 by Roberto Puzzanghera 12 comments
Feb 12, 2024: Roundcube webmail bug now exploited in attacks. It is sufficient to update Roundcube to the latest version.
- Info: https://roundcube.net
- Version: 1.6.6
Roundcube is a full featured webmail with a nice interface.
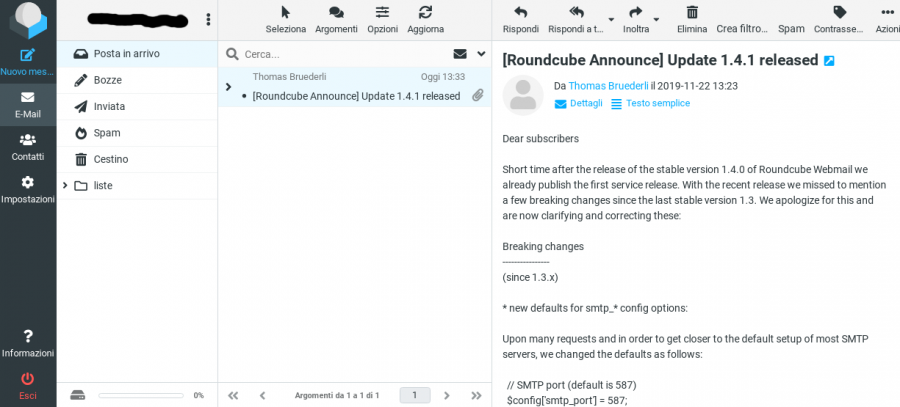
Changelog
- Gen 21, 2024
RC upgraded to v. 1.6.6
-new $config['imap_host'] variable
-all my SMTP config options were stripped from my configuration file and I had to restore them - Jan 3, 2021
disabled the SMTP authentication when sending messages via RC. SMTP port changed to 25.
Read the release note at https://github.com/roundcube/roundcubemail/blob/master/CHANGELOG.md for more info.
Patching qmail
February 12, 2024 by Roberto Puzzanghera 510 comments
- Latest stable version 2024.02.12 (github)
- Releases
- Changelog
- Readme
For my convenience I moved the qmail sources to my github space. Nonetheless, all information about qmail and related programs will continue to be posted in this web space, and this pages remain the place to eventually seek support. From now on, instead of releasing a combined patch for qmail, I'll release a package which is the result of the ancient netqmail-1.06 plus the patches and modifications listed below.
Changelog
WARNING: IF YOU ARE UPGRADING qmail AND YOU ARE USING A VERSION BEFORE 2024.01.11, BE AWARE THAT dk-filter HAS BEEN DROPPED, SO YOU HAVE TO RECONFIGURE DKIM AND MODIFY YOUR rc FILE ACCORDINGLY.
- Feb 12, 2024
- DKIM patch upgraded to v. 1.48
* fixed minor bug using filterargs for local deliveries (commit)
- Fixed several compilation warnings (commit)
- Fixed incompatible redeclaration of library function 'log2' in qmail-send.c qsutil.c as showed by notqmail friends here
- removed FILES, shar target from Makefile - Feb 6, 2024
- DKIM patch upgraded to v. 1.47
* fixed a bug which was preventing filterargs' wildcards to work properly on sender domain - Jan 20, 2024 (diff here)
liberal-lf: bare LF are no longer allowed by default due to smuggling vulnerability CVE-2023-51765. Bare LF can be allowed by defining ALLOW_BARELF in the tcprules or in the run file. - Jan 15, 2024
TLS patch by F. Vermeulen upgraded to version 20231230 (more info at https://inoa.net/qmail-tls/ tx Greg Bell for the patch)
- support to openssl 3.0.11 - Jan 11, 2024
- dkim patch upgraded to version 1.46
* dk-filter.sh has been dropped. If signing at qmail-remote level, before upgrading, you have to review the configuration.
- The variables USE_FROM, USE_SENDER and DKIMDOMAIN have been dropped
- when signing at qmail-remote level qmail-dkim now has to be called directly by spawn-filter in the rc file. man spawn-filter for more info
- In case of bounces the signature will be automatically based on the from: field. This will solve issues of DMARC reject by google in case of sieve/vacation bounces.
- In case of ordinary bounces (mailbox not found, for instance) the bounce domain will be taken from control/bouncehost and, if doesn't exist, from control/me - Dec 9, 2023
- sources moved to github.
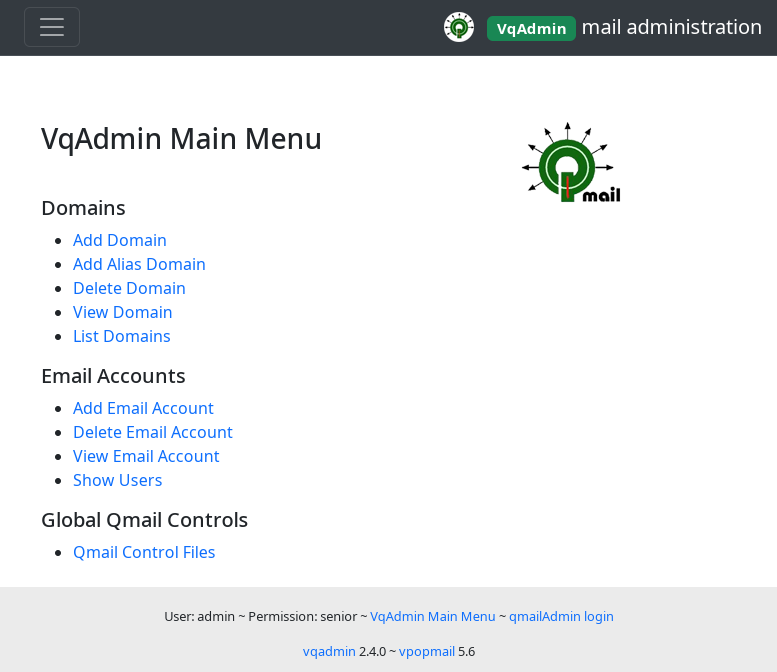
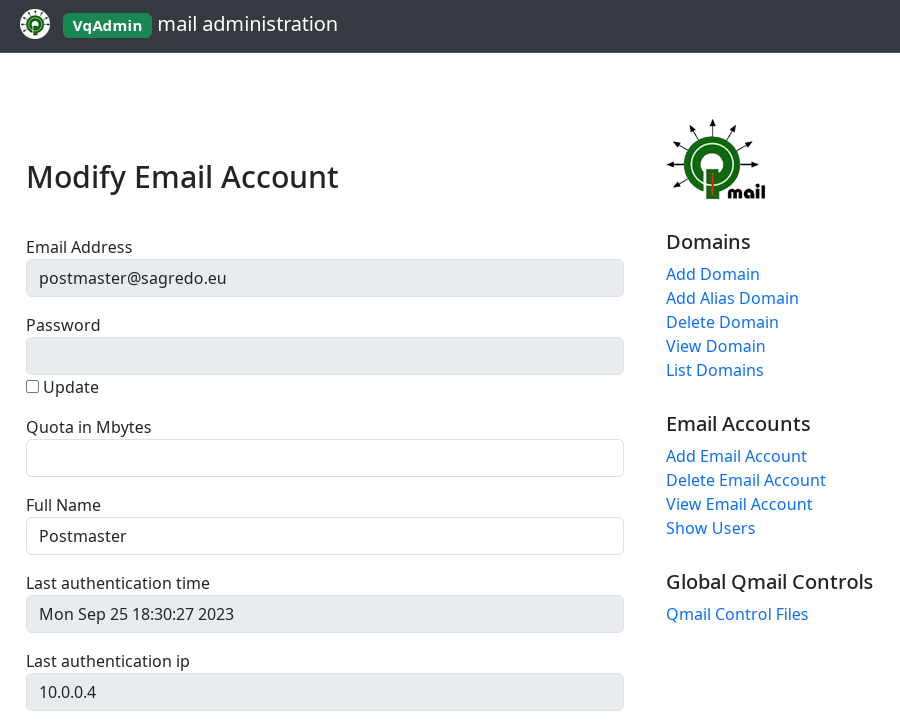
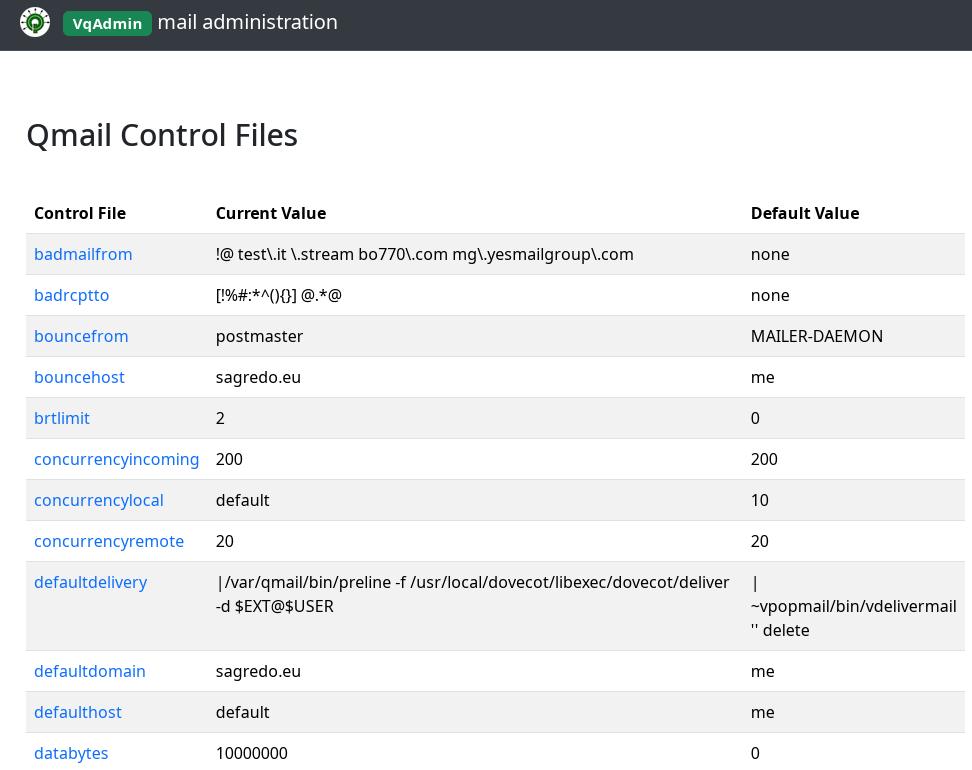
VqAdmin
January 19, 2024 by Roberto Puzzanghera 34 comments
- Original author: Inter7
- Version 2.4.0
- Changelog
- Download from github
- My old patches
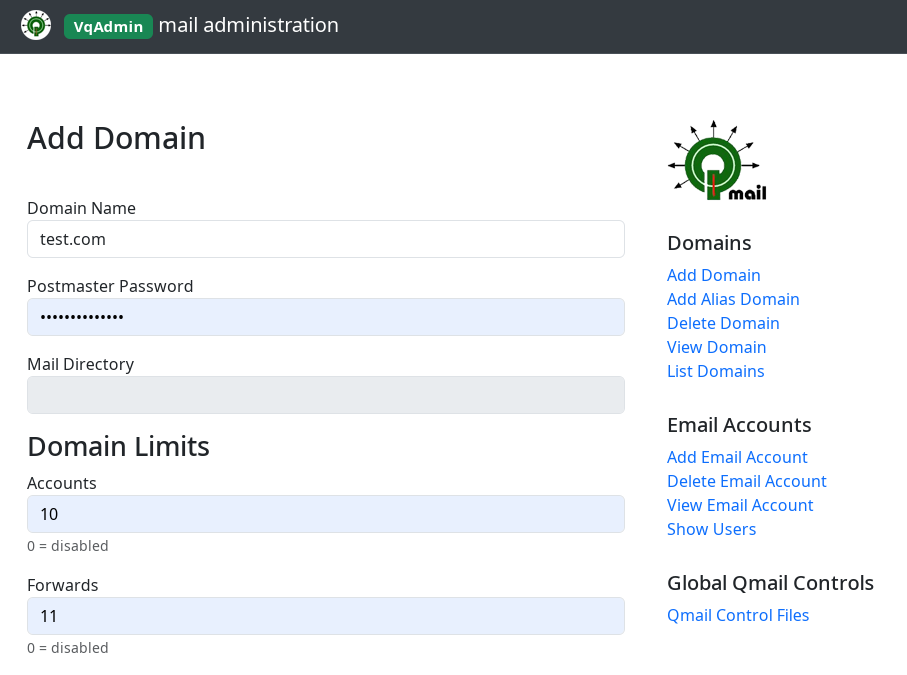
vqadmin is a web based control panel that allows system administrators to perform actions which require root access — for example, adding and deleting domains.
As you can see, VqAdmin has a new version with a new skin, all my patches (with ALI's patch included) and a lot of work in polishing the code. I also solved all autotools and gcc compilation warnings and changed a couple of things in order to rebuild the HTML theme (have a look at the changelog for more details). As always, your contributions in the comments are welcome.
PS: the apache side has some modification as well.
Have fun!
Changelog
- Mar 5, 2024
- version 2.4.0 marked as stable - Jan 19, 2024
- version 2.4.0-beta.2
* fixed a buffer overflow in domain.c (tx Bai Borko)
* solved -Wstringop-truncation warnings in domain.c and lang.c - Dec 21, 2023
- 2.4.0-beta released
- vqadmin moved to github - Jul 18, 2023
patch updated
- Italian translation file html/it updated, following the patch by Ali Erturk TURKER
- the vqadmin source directory has been cleaned of unnececessary files - Feb 18, 2023
Added Ali Erturk TURKER's patch to my combo. Original patch here
Installing and configuring vpopmail
January 11, 2024 by Roberto Puzzanghera 126 comments
- Inter7's original page
vpopmailversion: 5.6.1 (merged with my combined patch v. 2023.11.11)- Download from github/brunonymous
- My github on sagredo-dev/vpopmail (post here pull requests concerning my patches)
- More info here
- README.vdelivermail
Vpopmail provides an easy way to manage virtual email domains and non /etc/passwd email accounts on your mail servers.
Update as of December 11, 2023
Thanks to TLK Games guys at https://github.com/brunonymous/vpopmail we have a new vpopmail-5.6.0 version. They did a huge job merging together the old vpopmail-5.4.33 version with many patches that can be found around the net, my combo included. More importantly, they polished and corrected the code and added several features that you can see in the changelog.
From now on, I'll no longer release a new patch but I'll pull a request there, where you can get the released package.
For any request concerning my patches, this page remains the place where to find more information and ask for support. If you want to contribute to the code of my patches, you can send it here in a comment or post a PR in my github space (we don't want to bother our french friends with issues concerning my patch, ok?).
Changelog
- Jan 11, 2024
- vmysql.c: allow the insertion of a second valias row with the same alias/domain when vpopmail is configured with --enable-defaultdelivery and --enable-valias
- bug fix in mysql.h: wrong definition of VALIAS_TABLE_LAYOUT as it was looking for DEFAULTDELIVERY definition instead of DEFAULT_DELIVERY. This bug was preventing the correct auto creation of the valias table in MySQL
- configure.ac: solved all autoconf warnings - Dec 11, 2023
- patch merged with github/brunonymous
- vpopmail-5.6.0 released (read the upgrading notes) - Nov 11, 2023
- defaultdelivery patch: vmakedotqmail won't create users' .qmail if control/defaultdelivery already has vdelivermail. - Oct 23, 2023
- defaultdelivery patch: .qmail file won't be created if control/defaultdelivery already has vdelivermail
- Sep 5, 2023
- changed configuration option--enable-logging=e(wasp). Now failed attempts will be logged with no password shown. - Aug 27, 2023
- new combined patch. More info here
* The logic of the defaultdelivery patch/feature has been revised. If configured with--enable-defauldelivery vpopmailwill save control/defauldelivery in the user's .qmail andvdelivermailLDA in the domain's .qmail-default file. This will achieve multiple benefits: you haveqmailforwards andsievetogether andvaliasavailable. Thevaliastable schema was changed as well.
Source code moved to github
December 11, 2023 by Roberto Puzzanghera 0 comments
For my work convenience, I moved the source code of daemontools, qmail, vpopmail, qmailadmin simscan and VqAdmin to github. From now on, instead of releasing new patches of those programs I'll publish a package there. Nonetheless this web space remains the place where to find more information and ask for support. You'll notice that issues on my github spaces are disabled because I prefer to centralize the discussions here.
vpopmail will be grabbed from https://github.com/brunonymous/vpopmail. They did a huge job releasing a new vpopmail version with many patches, mine included. More importantly, they polished and corrected the code and added several features that you can see in the changelog.

SQL valias with sieve solution for qmail. New patches and Roundcube plugin
November 5, 2023 by Roberto Puzzanghera 6 comments
Changelog
- Jan 10, 2024
- fixed a bug in vpopmail which was preventing the correct auto creation of the valias table in MySQL - Nov 5, 2023
-bug fix: vpopmail defaultdelivery patch: it won't create the .qmail file in case control/defaultdelivery already has vdelivermail, in order to prevent a vpopmail loop
-qmailforward RC plugin: it won't create the copy record if $config['qmailforward_defaultdelivery'] contains 'vdelivermail'
Among the various problems that I set out to fix sooner or later, I think I've finally solved one: the impossibility of having the vpopmail aliases saved in the database (--enable-valias) and the sieve rules at the same time.
But before presenting the solutions, let's clarify the problem to be solved, which has also been discussed in several threads of this blog. It is no coincidence that the solution I identified was partly inspired by the (re)reading of some of the visitors posts.
The problem
Usually vpopmail copies its delivery agent (vdelivermail) into the .qmail-default file of newly created domains. This makes it impossible to use Dovecot filters based on sieve rules, as this would require Dovecot-LDA.
On the other hand, if we set the Dovecot delivery agent to .qmail-default in order to have the sieve rules, when the user uses the Dovecot filters to generate a forward (s)he will unintentionally cause the violation of the SPF, because qmail is out of the question and srsfilter cannot be launched to rewrite the sender's address.
The best thing would be for the user to manage the aliases via dot-qmail, but this can only be done by the domain administrator, while the aliases stored on SQL database are not an option, as Dovecot has nothing to do with them.
These are problems that we know well due to the protest emails of users who see their forwarding messages bounced back because of the SPF/DKIM/DMARC check failure. But now we're going to fix it once and for all :-)
Installing a Let's Encrypt certificate for your qmail, dovecot and apache servers
August 6, 2023 by Roberto Puzzanghera 26 comments
Changelog
- Aug 6, 2023
The certificates installation is now based ondehydrated.The previous documentation based oncertbotwill be left as is at the bottom of this page, but it won't be updated anymore. - May 18, 2023
added the option--key-type rsato thecertbotcommand, to avoid thatcertbotwill silently default toECDSAthe private key format, which results not understandable by myopenssl-1.1. In this way the format of the private key will beRSA. More info here.
To enable HTTPS on your website, you need to get a certificate (a type of file) from a Certificate Authority (CA). Let’s Encrypt is a CA. In order to get a certificate for your website’s domain from Let’s Encrypt, you have to demonstrate control over the domain. With Let’s Encrypt, you do this using software that uses the ACME protocol which typically runs on your web host.
Upgrading notes
In case you have to replace a working installation of certificates based on certbot, you don't need to take any precautions as they won't be overwritten by the new ones generated by dehydrated. Therefore it is possible to run our tests on the production server itself. Of course it will be good to use a test domain while tinkering with Apache.
dehydrated installation
- github dehydrated page
- AlienBob article (for
Slackwareusers, but the informations are generic and suitable for allLinuxdistributions)
Dehydrated is a client for signing certificates with an ACME-server (e.g. Let's Encrypt) implemented as a relatively simple (zsh-compatible) bash-script. This client supports both ACME v1 and the new ACME v2 including support for wildcard certificates!
dehydrated is a simple shell program that requires no dependencies, unlike the official certbot program, which needs a very long set of python libraries. Maintaining all this volume of programs proved to be quite time expensive, which is why I decided to switch to dehydrated.